So you’re out and about and require connectivity back home or SOHO. Here is your pptp vpn solution, for free
An elegant solution has been around for the DDWRT, the distro specialising on your Linksys 54GL routers. I initially found this to not be so well documented.
This will essentially turn your 54gl box into a pptp vpn gateway in 5 steps. These boxes are smart in the sense that you can bind multiple to a client-server level but for the time being we’ll look at giving you access from an internet bound PC or your smart phone. I will put further information up showing you how to go about setting up your computer, smartphone, or tablet.
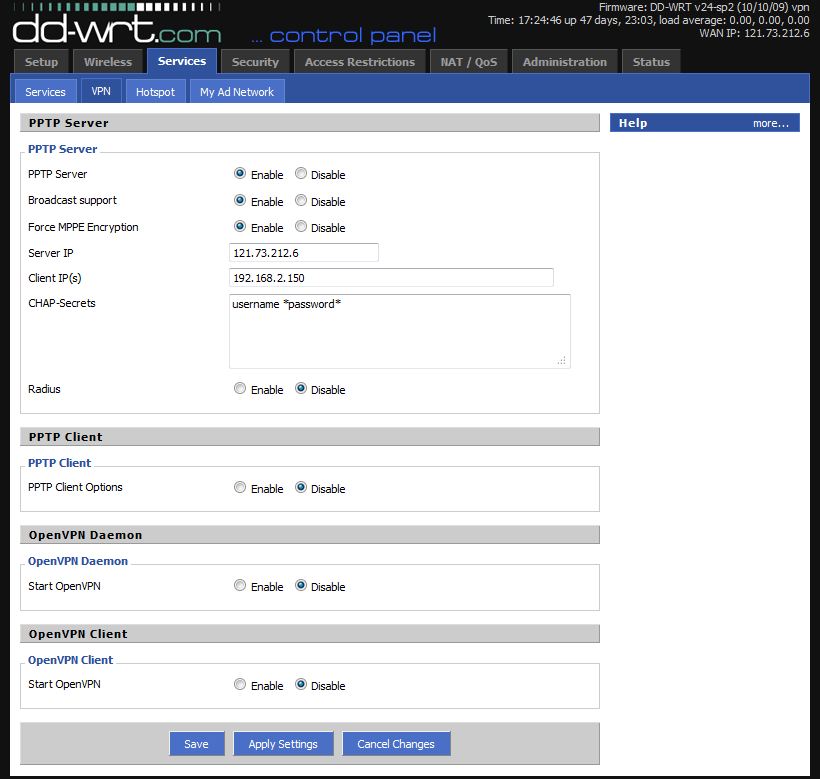
For the time being, what we are interested in enabling is the PPTP VPN Server.
Secondly – “Force MPPE Encrytion” – this will force your connecting client machines to use encryption.
Note: Forcing MPPE encryption is by no means public or private key encryption so if the attacker is smart enough they will still be able to play a man-in-the-middle role in a attack.
Server IP – this will be your external facing IP address/your internet address.
Client IP(s) – here you can use a single IP or a DHCP range. For example for example 192.168.2.150,192.168.2.150-155.
CHAP Secrets – this will be your usernames and passwords that are allowed to VPN into your netwrok – the format follows:
username *password* IE – joeblogs *password123*
Last note: the subnet you are connecting from will need to be different to the destination. IE You cannot connect from private 192.168.y.0 to 192.168.y.0 but you can 192.168.1.0 to 192.168.0.0
For the upcoming blog I will be looking at setting up your client end on Windows 7 and Android phone. Pretty neat solution if you’re needing a pptp vpn server setup in 5 minutes.